ICS Devices Vulnerable to Side-Channel Attacks: Researcher Shows
(Eduard Kovacs – SecurityWeek) Side-channel attacks can pose a serious threat to industrial control systems (ICS), a researcher warned last month at SecurityWeek’s ICS Cyber Security Conference in Atlanta, GA.
Demos Andreou, a lead engineer at power management company Eaton, has conducted an analysis of protection devices typically used in the energy sector, specifically in power distribution stations.
Side-channel attacks can be used to extract data from a system based on information gained by observing its physical implementation. There are several side-channel attack methods, but Andreou’s research looked at timing and power analysis attacks. These rely on the analysis of the time it takes to execute various computations, and the measurable changes in power consumption as the targeted device performs cryptographic operations, respectively.
The researcher says both timing and power analysis attacks can be launched against ICS devices. However, since timing attacks are easier to detect and block, he focused his research on power analysis.
While side-channel attacks have been known for a long time, few research papers describe their impact on industrial systems. It’s worth noting that the notorious Meltdown and Spectre side-channel attacks also affect ICS, but those methods involve only software and they rely on speculative execution, which helps speed up execution in modern CPUs.
Andreou told SecurityWeek in an interview that his goal is to raise awareness of the risks, show that attacks are not just theoretical, and that they could be conducted even with limited resources.
As part of his work at Eaton, Andreou conducts research into compliance and ethical penetration testing of industrial control systems and networks. Andreou and others help Eaton ensure that its products are secure and customer networks are not vulnerable to cyber threats.
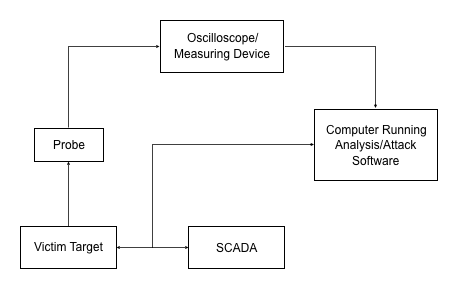
Power analysis attacks rely on the power consumption changes of semiconductors during clock cycles, the amount of time between two pulses shown by an oscilloscope. The signals form a power profile, which can provide clues on how the data is being processed.
For example, a password can be obtained one character at a time by observing the power profile when a correct character has been entered compared to an incorrect character. An encryption key can also be extracted using the same technique.
Andreou said he conducted successful experiments on protection devices from three major vendors, but he believes products from other companies are affected as well if the microprocessors they use are vulnerable to these types of attacks.
While the tested devices are 5-10 years old, the researcher says newer products likely have the same vulnerabilities, as these types of attacks were until recently only theoretical and it’s unlikely that vendors took measures to mitigate the risks. The availability of open source software and inexpensive hardware have made it much easier to conduct side-channel attacks.
Andreou showed that an attacker who has physical access to protection devices can use an oscilloscope and a specialized hardware device running open source software to obtain an encryption key. The hardware required for such attacks costs roughly $300, the researcher said.
In the case of the analyzed protection devices, an attacker can extract the encryption key and use it to make configuration changes. Since these systems are used to protect the power grid, changing their settings can have serious consequences, Andreou told SecurityWeek.
A malicious actor could cause the system to fail or have it send false data back to its operator. These devices are distributed and they are controlled by a master system. Incorrect readings from one device can have repercussions for a different part of the network.
Furthermore, the researcher explained, an attacker could make configuration changes that are not immediately obvious. For instance, some of the analyzed protection devices have different settings for different seasons and a hacker could ensure that the changes they make would only go into effect when a certain season starts, which would disguise the attack.
Power analysis attacks can pose a serious threat because they are practically impossible to detect, as an attacked device could seemingly continue performing its normal operations even after it has been compromised, the researcher explained.
Conducting such attacks in a real-world scenario is not an easy task, but it’s not impossible. Andreou pointed out that it may not be difficult to obtain physical access to such devices as they are often left unsupervised. Malicious insiders, consultants, and repair centers could have plenty of opportunities to launch an attack.
On the other hand, the attack must be launched — i.e., the power consumption must be measured — exactly when the device performs an operation that involves the targeted crypto key. This requires reverse engineering the device and knowing ahead of time what type of product is targeted.
Conducting an attack could take hours, most of which involves physical preparation (e.g., opening the targeted device, connecting sensors). The software part of the attack is much faster and the key can be obtained in a matter of minutes.
For instance, if the Advanced Encryption Standard (AES) is used, the attacker can extract the key one byte at a time. In the case of AES-128, all they need to do is go through combinations from 00 to 255 for each of the 16 characters of the encryption key and monitor power profiles for each attempt.
Additional technical details on the attack are available in Andreou’s presentation at the ICS Cyber Security Conference:
Side Channel Attacks Against ICS Devices from SecurityWeek on Vimeo.
Related: Flaws Expose Siemens Protection Relays to DoS Attacks
Related: Risks to ICS Environments From Spectre and Meltdown Attacks
Side-Channel Attacks Put Critical Infrastructure at Risk
ICS Devices Vulnerable to Side-Channel Attacks: Researcher Shows (Eduard Kovacs - SecurityWeek) Side-channel attacks can pose a serious threat to industrial control systems (ICS), a researcher warned last month at SecurityWeek’s ICS Cyber Security Conference in Atlanta, GA. Demos Andreou, a lead engineer at power management company Eaton, has conducted an analysis of protection devices typically used in the energy sector, specifically in power distribution stations. Side-channel attacks can be used to extract data from a system based on information gained by observing
Siemens Warns Customers of New Meltdown, Spectre Variants
(Eduard Kovacs - SecurityWeek) - Siemens recently updated its security bulletin for the Meltdown and Spectre vulnerabilities to inform customers of the latest variants, specifically the ones known as LazyFP and Spectre 1.1. Several industrial control systems (ICS) vendors published security advisories for the CPU flaws shortly after they were disclosed in early January. Siemens published a bulletin on speculative side-channel vulnerabilities on January 11. In late May, the company updated its bulletin to include information about Variant 3a and Variant 4,
Vulnerabilities Expose Siemens Central Plant Clocks to Attacks
(SecurityWeek - Eduard Kovacs) Siemens informed customers on Tuesday that some of its SICLOCK central plant clocks are affected by several vulnerabilities, including ones that have been rated “critical.” Siemens SICLOCK devices are used to synchronize time in industrial plants. The central plant clock ensures stability in case of a failure or loss of reception at the primary time source. According to the German industrial giant, SICLOCK systems are affected by a total of six vulnerabilities. The security holes have been assigned
Siemens Fixes Vulnerabilities in SIMATIC, License Manager Products
(SecurityWeek) - Siemens has released software updates to address several vulnerabilities in its SIMATIC and Automation License Manager (ALM) products. According to advisories published last week by both ICS-CERT and Siemens, the ALM, which allows customers to centrally manage licenses for their Siemens products, is affected by three vulnerabilities. The security holes, including one rated high severity and one rated critical, were reported to the vendor by researchers from Kaspersky Lab’s critical infrastructure team. The critical vulnerability, tracked as CVE-2016-8565, is a



